E-commerce optimization for high-traffic events is crucial! Prepare your online store for surges. Learn performance optimization tips to handle peak seasons
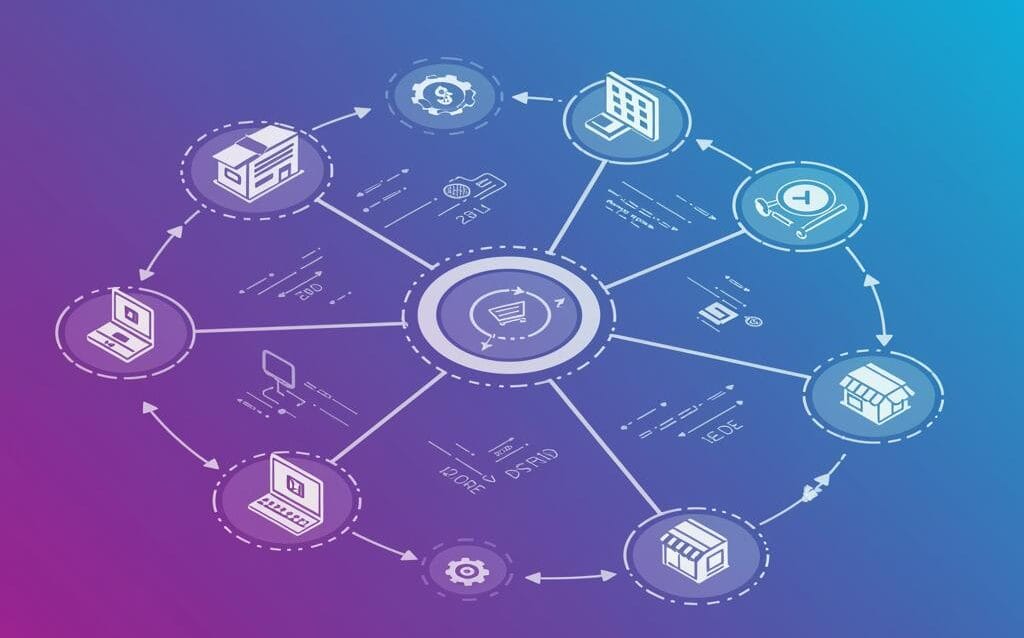
Omnichannel Inventory: Tech Implementation Guide
Master omnichannel inventory management! Our tech implementation guide simplifies the process, ensuring seamless stock visibility & optimized fulfillment
E-commerce Security: PCI DSS Compliance Implementation Guide
Secure your online store! This PCI DSS Implementation Guide simplifies e-commerce security compliance. Learn step-by-step how to protect customer data and
Payment Gateway Comparison: Find the Best Fit for Your Business
**Payment Gateway Comparison:** Unsure which payment gateway suits your business? Our comparative analysis simplifies selection for various business types
E-commerce Microservices: Ditch the Monolith for Scalability
Ditch the e-commerce monolith! Learn how microservices architecture boosts scalability, improves agility, and unlocks innovation. Explore breaking down your e
Headless Ecommerce: Benefits & Challenges Explained
Unlock the power of **headless ecommerce**! Explore its benefits, from enhanced flexibility to improved customer experiences. Learn about implementation
Hybrid Work Tech Stack: Tools for Modern Workplace
Optimize your hybrid work tech stack! Discover essential tools for seamless collaboration, communication, & productivity in the modern workplace. Learn more!
Tech Cost Optimization: Sustainable IT Spending Framework
**Tech Cost Optimization:** Reduce IT spending without sacrificing innovation. Our sustainable framework helps you optimize technology costs for long-term
CIO Dashboard: Key Metrics for Tech Leadership
**CIO Dashboard:** Get the key metrics tech leaders need! Track performance, manage resources, and drive strategic decisions with our essential CIO dashboard
Citizen Development Governance: No-Code Risk Management
Unlock the power of citizen development governance! Mitigate no-code risks & empower innovation safely. Learn how to manage citizen development projects