North Korean threat groups, linked to the country’s cyber-operations, are increasingly employing living-off-the-land (LotL) techniques and leveraging trusted services to evade detection. A recent campaign, dubbed “DEEP#DRIVE” by security firm Securonix, showcases the threat group’s use of PowerShell scripts and storing data in Dropbox folders, while also demonstrating improved operational security.
The DEEP#DRIVE campaign involved the use of fake work logs, insurance documents, and cryptocurrency-related files to trick users into downloading and running a zipped shortcut file. This file gathered system configuration information and executed PowerShell and .NET scripts, which uploaded the system data to Dropbox folders and downloaded additional commands for further compromise.
While the attackers showed interest in quick financial gains, such as targeting cryptocurrency users, their primary focus was on stealing sensitive data from South Korean government agencies and businesses, according to Tim Peck, a senior threat researcher at Securonix.
“We observed evidence of both espionage and financial motivation, although the focus was more on espionage,” he says. “This aligns with Kimsuky’s historical targeting of South Korean government agencies, enterprises, and strategic industries.”
North Korean cyber-operations groups have consistently targeted South Korea and the US, with South Korean government agencies and companies being among the most popular targets. In September 2024, the FBI warned that North Korean groups planned to launch a surge of attacks against organizations with significant cryptocurrency reserves, and Kimsuky launched a similar multistage attack against South Korean targets last year.
A Prolific Group
Kimsuky is not a monolithic group but comprises five threat groups with overlapping activities, according to threat intelligence firm Recorded Future. One group focuses on the healthcare and hospitality sectors, while another targets cryptocurrency markets.
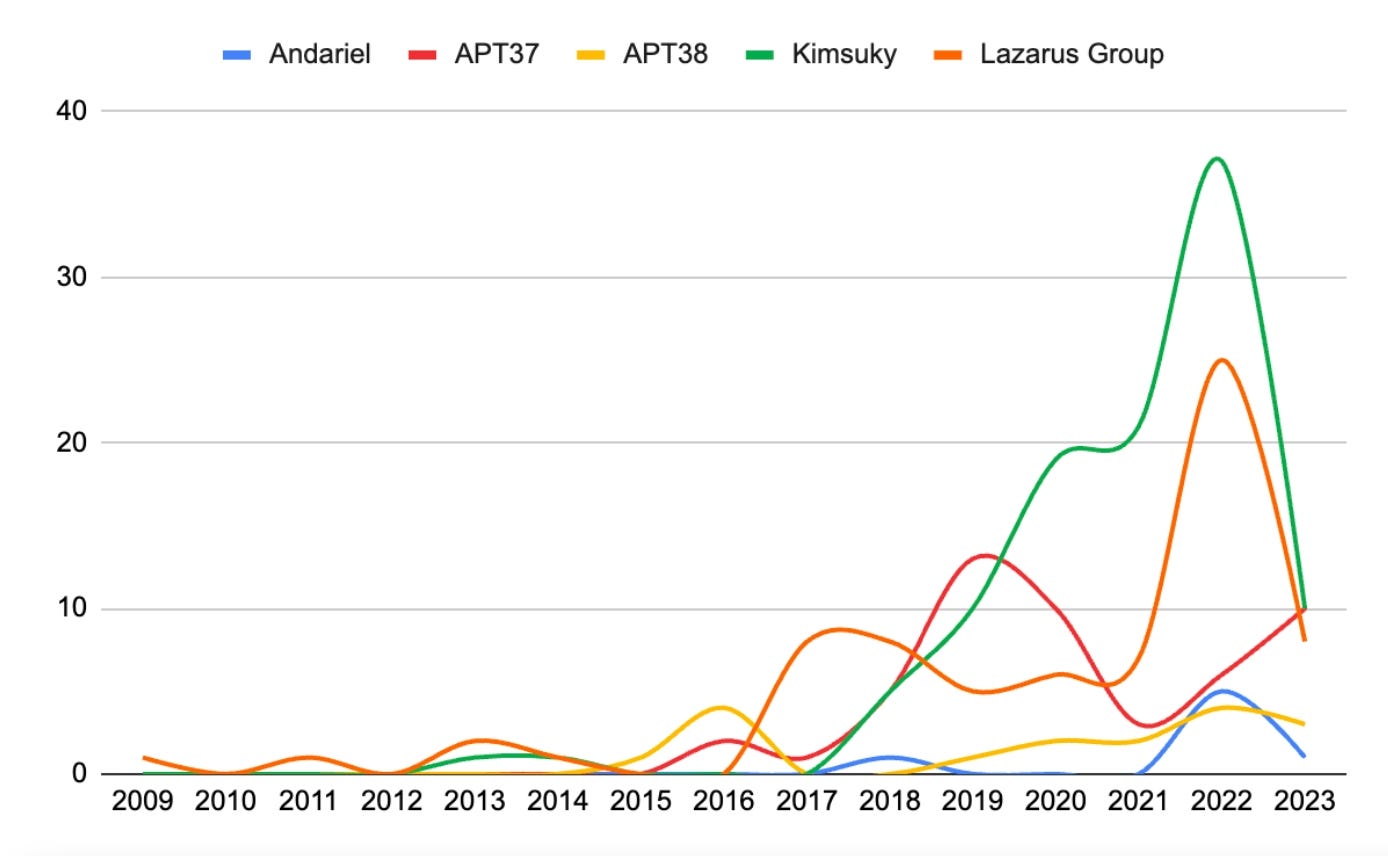
By mid-2023, Kimsuky became the most prolific North Korean group. (More recent data not available.) Source: Recorded Future’s “North Korea’s Cyber Strategy” report
The Kimsuky groups accounted for the most attacks identified as North Korean in origin between 2021 and 2023, according to Recorded Future’s “North Korea Cyber Strategy” report. In 2024, the groups continued to account for a high volume of attacks, says Mitch Haszard, senior threat intelligence analyst with Recorded Future.
“These groups conduct high-volume phishing campaigns, primarily targeting individuals and organizations in South Korea, while occasionally targeting entities in other countries,” he says. “In the activity we see, these groups appear to be going for volume, rather than more time-consuming, tailored spear-phishing operations.”
Other well-known North Korean groups, such as Lazarus and Andariel, are not as prolific as the Kimsuky threat actors. While some of those groups focus on gathering sensitive information, nearly all also have a financial motivation.
Thousands of Victims?
In the DEEP#DRIVE campaign, the Kimsuky group’s attack scripts uploaded data on the system configuration to one of several Dropbox folders. While the Securonix researchers were not able to gather intelligence from all the suspected Dropbox locations, they uncovered signs of more than 8,000 configuration files, although some appear to be duplicates, Peck says.
While that means they likely came from the same victim organizations, the campaign appears to be quite successful, he says.
“There were two factors which contributed to the ‘uniqueness’ of the configuration file, the username, and IP address,” Peck says. “Some usernames were associated with dozens of similar IP addresses, which could indicate lateral movement by the attacker — [that is], infecting dozens of machines from the same entity.”
The data from a compromised system includes the host IP address, the system uptime, details about the OS type and version, any installed security software, and a list of running processes.
Kimsuky Improves Its OpSec
The campaign also highlighted North Korean cyber-operations groups’ improvements to operational security. The group used OAuth-based authentication on its Dropbox folders, preventing traditional URL-blocking or network-based defenses from following the links. The threat actors also quickly took down components of their infrastructure soon after the Securonix researchers began investigating, Securonix’s Peck says.
“This level of operational awareness is not always present in phishing-driven malware campaigns,” he says.
For companies, the threat group’s tactics underscore that hidden file extensions should be disabled, shortcut files should be blocked from executing in user folders, and only signed PowerShell scripts should be allowed to execute. Those three countermeasures make the attackers’ activity much easier to detect, Peck says.
In addition, companies in targeted industries — such as cryptocurrency exchanges and government agencies — should bolster their email security and regularly train employees on how to spot phishing threats, says Recorded Future’s Haszard.
“Most North Korean cyberattacks still start with social engineering and a phish,” he says. “Companies should ensure that they have an email security solution in place and regularly train employees on phishing threats, as well as conduct simulated phishing tests.”
Source Link