Here is a rewritten version of the content:
The Rise of PDF-Based Attacks: Understanding the Threat
Over 400 billion PDFs were opened last year, and 16 billion documents were edited in Adobe Acrobat. With 87% of organizations using PDFs as a standard file format for business communication, it’s no wonder that malicious PDFs have become a prime target for cybercriminals. In fact, PDF-based attacks now account for 22% of all malicious email attachments, according to Check Point Research.
While 68% of malicious attacks are delivered through email, PDF-based attacks are particularly insidious for businesses that share large quantities of these files. Threat actors have begun leveraging their deep understanding of how security providers scan and analyze files, and PDFs are becoming a preferred entry point due to their high success rate. These attacks use sophisticated countermeasures to bypass detection, making them increasingly hard to spot – and stop.
Understanding Why PDFs Are a Prime Target for Cybercriminals
PDFs are complex, with the PDF specification spanning nearly 1,000 pages. This complexity opens the door to numerous attack vectors that some security systems are ill-equipped to detect. PDFs act like CAPTCHA tests, designed to lure human victims while being evasive to automated detection systems. The unique combination of simplicity for the user and complexity for security systems makes malicious PDFs so attractive to bad actors.
In the past, cybercriminals used known vulnerabilities in PDF readers to exploit flaws in the software. However, as PDF readers have become more secure, this attack method is less reliable. Attacks relying on JavaScript or other dynamic content embedded within PDFs have also become less common, as they are more easily detected by security solutions.
The Evolution of PDF-Based Attacks
Threat actors have shifted tactics, relying on social engineering to deceive recipients. PDFs are widely regarded as safe and reliable, making them ideal for hiding malicious code or links. By taking advantage of users’ familiarity with PDF attachments, attackers boost their chances of deceiving recipients. PDFs can slip past email security systems that focus on flagging threats in other types of files.
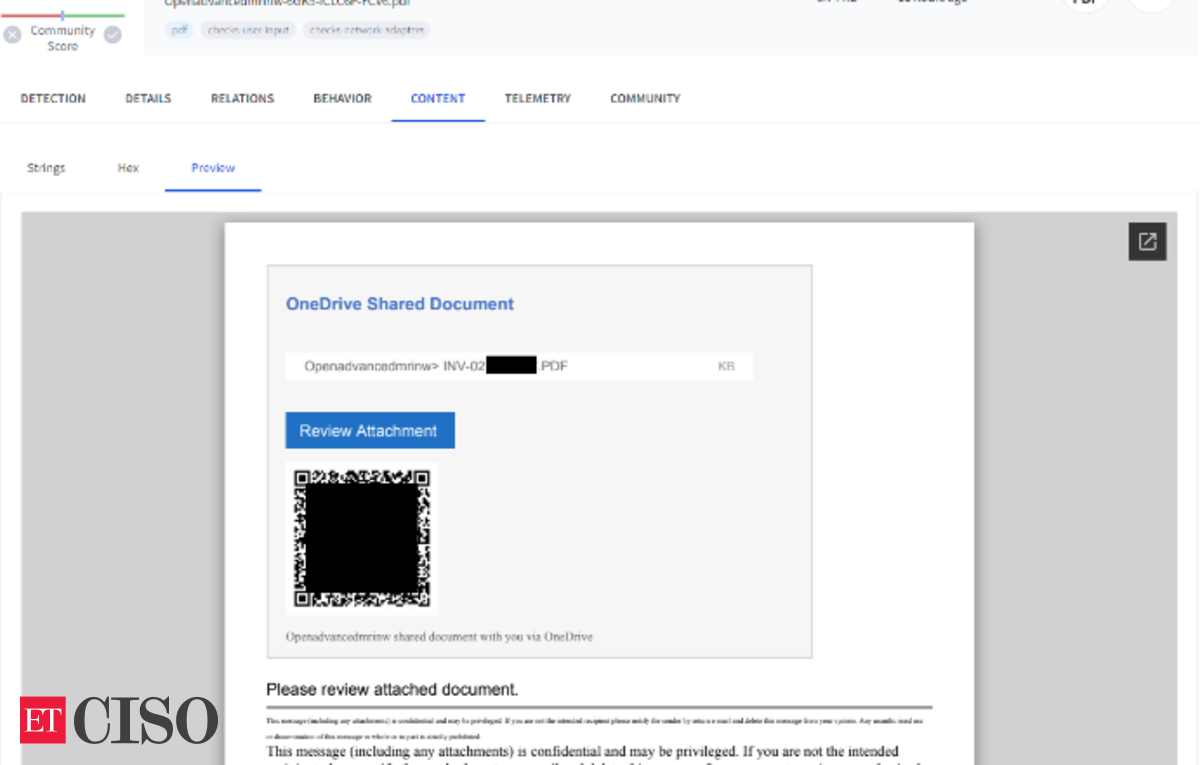
One common technique involves embedding links in PDFs that lead to malicious websites or phishing pages. While this technique is relatively low-tech, its simplicity makes it harder for automated systems to detect. The attacker’s goal is to get the victim to click the link, thus starting the attack chain.
The Anatomy of a PDF Attack Campaign
Check Point Research has observed link-based campaigns as one of the most common PDF attack techniques. These campaigns are simple yet effective, typically involving a PDF with a link to a phishing site or malicious file download. The link is often accompanied by an image or text designed to lure the victim into clicking it. These images often mimic trusted brands, making the file look benign at first glance.
What makes these campaigns difficult to detect is that the attackers control all aspects of the link, text, and image, making it easy to change any of these elements. This flexibility allows these attacks to be resilient against reputation-based security tools or those that rely on static signatures.
Evasion Techniques Used by Threat Actors
Threat actors continuously adapt their techniques to evade detection by security systems. These techniques show a deep understanding of how different detection methods work and are often tailored to bypass specific tools.
- URL Evasion Techniques: Attackers use benign redirect services, QR codes, or phone scams to mask the true destination of the malicious link.
- Static Analysis Evasion: PDFs have a complex structure, and many security tools rely on static analysis to detect malicious activity. However, this method is not always effective against sophisticated PDF-based attacks.
- File Obscurement: PDFs can be heavily obfuscated, making it difficult to detect malicious behavior. Attackers use encryption, filters, and indirect objects to hide their true intentions.
- Machine Learning Evasions: As security systems rely on machine learning to detect threats, attackers are finding ways to evade these models. One common technique is embedding text in images rather than using standard text formats.
How to Stay Safe from PDF-Based Attacks
Check Point Threat Emulation and Harmony Endpoint deliver robust protection against diverse attack tactics, file types, and operating systems. However, there are practical steps everyone can take to reduce risk:
- Double-check the sender’s email address, even if the PDF looks legitimate.
- Be cautious with attachments, especially if you weren’t expecting a PDF.
- Hover over links to see the full URL and be cautious of shortened links or those using redirect services.
- Keep your browser, PDF reader, and antivirus software up to date.
- Disable JavaScript in PDF viewers unless absolutely necessary.
- Keep your operating system and security tools updated to patch vulnerabilities exploited in malicious PDFs.
By understanding the tactics used by threat actors and taking these practical steps, you can reduce the risk of falling victim to a PDF-based attack.
Published On Apr 5, 2025 at 08:55 AM IST
Source Link